Small Business CRM Security in 2025: Protecting Your Data and Building Customer Trust
Small Business CRM Security in 2025: A Comprehensive Guide
The world of small business is constantly evolving. We’re seeing incredible innovation, fierce competition, and a relentless need to adapt. At the heart of many successful small businesses lies a Customer Relationship Management (CRM) system. It’s the central nervous system, the engine that drives interactions, sales, and ultimately, growth. But as we head towards 2025, a critical aspect of your CRM strategy demands careful attention: security. This isn’t just about compliance; it’s about safeguarding your business’s most valuable asset: your customer data and your reputation.
This guide will delve deep into the crucial aspects of small business CRM security in 2025. We’ll explore the current threat landscape, the specific vulnerabilities you need to be aware of, and the practical steps you can take to protect your data, your customers, and your business. Prepare to fortify your CRM and build a foundation of trust that will carry you through the coming years.
Understanding the CRM Security Landscape in 2025
The threats to your CRM data are more sophisticated and pervasive than ever before. Gone are the days when a simple firewall was enough. Cybercriminals are incredibly resourceful, constantly developing new tactics and exploiting vulnerabilities. Let’s break down the key elements of this evolving landscape:
The Rise of Sophisticated Cyberattacks
In 2025, the attacks are less about brute force and more about precision. We’re seeing a surge in:
- Phishing 2.0: Spear phishing attacks, specifically tailored to your employees, will become even more convincing. Hackers will leverage social engineering, gathering information from social media and other sources to craft incredibly realistic emails and messages. Think of it as a digital Trojan horse, designed to trick your team into revealing sensitive credentials or clicking malicious links.
- Ransomware Evolution: Ransomware remains a significant threat, but the tactics are changing. Cybercriminals are now targeting not just data, but also the availability of your CRM system itself. Imagine your sales team locked out of their accounts, unable to access customer information, or close deals. That’s the devastating reality ransomware can create. They’ll also threaten to leak sensitive customer data publicly if the ransom isn’t paid, adding an extra layer of pressure and reputational damage.
- Supply Chain Attacks: Your CRM system relies on various third-party vendors and integrations. Hackers are increasingly targeting these vendors, knowing that a successful breach can provide access to multiple businesses. This means that your CRM’s security is only as strong as the weakest link in your supply chain.
- AI-Powered Attacks: Artificial intelligence is a double-edged sword. While it can be used to enhance security, it’s also being weaponized by cybercriminals. AI can automate attacks, making them faster, more efficient, and harder to detect. It can also analyze vast amounts of data to identify vulnerabilities and personalize attacks.
The Importance of Data Privacy Regulations
Data privacy regulations are becoming more stringent globally. The implications for small businesses are significant. Non-compliance can result in hefty fines, reputational damage, and a loss of customer trust. Key regulations to be aware of include:
- GDPR (General Data Protection Regulation): Even if your business isn’t based in Europe, if you have customers in the EU, you must comply with GDPR. This regulation sets strict rules about how you collect, store, and process personal data.
- CCPA (California Consumer Privacy Act) & CPRA (California Privacy Rights Act): These regulations give California residents significant rights regarding their personal data, including the right to access, delete, and opt-out of the sale of their data.
- Other State-Level Regulations: More and more states are enacting their own data privacy laws, creating a complex patchwork of regulations. Staying informed about these changes is crucial.
Compliance isn’t just a legal obligation; it’s a business imperative. Customers are increasingly concerned about their privacy and will choose to do business with companies they trust to protect their data.
The Human Factor: Employee Training and Awareness
No matter how sophisticated your security measures are, they’re only as effective as the people who use them. Human error is a leading cause of data breaches. That’s why employee training and awareness are absolutely critical. This includes:
- Phishing Awareness Training: Regular training to help employees identify and avoid phishing attacks. This should include simulated phishing exercises to test their vigilance.
- Password Security Best Practices: Training on creating strong, unique passwords and using a password manager. Multi-factor authentication (MFA) should be mandatory.
- Data Handling Procedures: Clear guidelines on how to handle customer data, including secure storage, access controls, and data disposal.
- Social Engineering Awareness: Educating employees about social engineering tactics and how to recognize them.
Key Vulnerabilities in Your CRM System
Understanding the specific vulnerabilities in your CRM system is the first step towards protecting it. Here are some of the most common areas of weakness:
Weak Passwords and Lack of Multi-Factor Authentication (MFA)
This is a fundamental vulnerability. Weak passwords are easy to crack, and without MFA, a compromised password can grant attackers full access to your CRM. MFA adds an extra layer of security by requiring users to verify their identity using a second factor, such as a code sent to their phone or a biometric scan.
Unsecured Integrations
CRM systems often integrate with other applications, such as email marketing platforms, e-commerce systems, and social media channels. If these integrations aren’t properly secured, they can create entry points for attackers. Ensure that all integrations are using secure protocols and that you’re regularly reviewing and updating them.
Lack of Regular Software Updates
Software vendors regularly release updates to patch security vulnerabilities. Failing to install these updates promptly leaves your CRM system exposed to known exploits. Automate your updates whenever possible and stay informed about security patches.
Insufficient Access Controls
Not all employees need access to all CRM data. Implement role-based access control (RBAC) to restrict access to sensitive information based on job roles and responsibilities. Regularly review user permissions and remove access for employees who no longer need it.
Data Backup and Disaster Recovery Failures
Data loss can be catastrophic. Regularly back up your CRM data and test your disaster recovery plan to ensure that you can restore your system in the event of a breach or other disaster. Consider offsite backups and data redundancy.
Insider Threats
Insider threats, whether malicious or accidental, can pose a significant risk. Implement measures to monitor user activity, detect suspicious behavior, and protect against data exfiltration. Conduct background checks on employees who handle sensitive data.
Implementing a Robust CRM Security Strategy for 2025
Building a strong security posture for your CRM requires a multi-layered approach. Here’s a practical roadmap:
1. Conduct a Comprehensive Security Assessment
Before you can fix the problems, you need to know what they are. A security assessment will identify vulnerabilities in your CRM system, your infrastructure, and your processes. This can be done internally or by hiring a third-party security expert. The assessment should include:
- Vulnerability Scanning: Using automated tools to identify known vulnerabilities in your software and hardware.
- Penetration Testing: Simulating a real-world attack to identify weaknesses in your security defenses.
- Risk Assessment: Identifying and prioritizing the risks to your CRM data and systems.
- Compliance Audit: Ensuring that your CRM practices comply with relevant data privacy regulations.
2. Strengthen Access Controls and Authentication
This is a foundational step. Implement the following:
- Enforce Strong Passwords: Require employees to use strong, unique passwords and regularly change them.
- Implement Multi-Factor Authentication (MFA): MFA should be enabled for all users, especially those with administrative access.
- Role-Based Access Control (RBAC): Grant access to data and features based on job roles and responsibilities.
- Regular User Access Reviews: Periodically review user permissions to ensure that they are still appropriate.
- Privileged Access Management (PAM): Consider PAM solutions to manage and secure privileged accounts.
3. Secure Your Data with Encryption
Encryption protects your data from unauthorized access, even if your system is breached. Implement the following:
- Data Encryption at Rest: Encrypt your CRM data while it’s stored on your servers or in the cloud.
- Data Encryption in Transit: Use secure protocols (e.g., HTTPS) to encrypt data as it’s transmitted between your users and the CRM system.
- Database Encryption: Encrypting the databases that store your customer data.
4. Implement Regular Data Backups and Disaster Recovery
Data backups are your lifeline in case of a breach, data loss, or other disaster. Establish the following:
- Automated Backups: Automate your data backups to ensure they are performed regularly.
- Offsite Backups: Store your backups in a separate location, such as the cloud, to protect against physical disasters.
- Backup Testing: Regularly test your backups to ensure that you can restore your data successfully.
- Disaster Recovery Plan: Develop a detailed disaster recovery plan that outlines the steps you will take to restore your CRM system in the event of a disaster.
5. Patch and Update Your Software Regularly
Keeping your software up-to-date is crucial for security. Implement the following:
- Automated Updates: Enable automated updates for your CRM software, operating systems, and other applications.
- Patch Management: Establish a patch management process to ensure that you are applying security patches promptly.
- Vulnerability Scanning: Use vulnerability scanning tools to identify vulnerabilities that need to be patched.
6. Monitor Your CRM System for Suspicious Activity
Monitoring your CRM system can help you detect and respond to security incidents quickly. Implement the following:
- Security Information and Event Management (SIEM): Consider using a SIEM solution to collect and analyze security logs from your CRM system and other sources.
- Intrusion Detection and Prevention Systems (IDS/IPS): Deploy IDS/IPS to detect and block malicious activity.
- User Behavior Analytics (UBA): Use UBA to identify unusual user behavior that may indicate a security threat.
- Log Management: Establish a log management process to collect, store, and analyze security logs.
7. Train Your Employees on Security Best Practices
Employee training is your first line of defense against many types of attacks. Provide ongoing training on the following topics:
- Phishing Awareness: Train employees to identify and avoid phishing attacks.
- Password Security: Teach employees how to create and manage strong passwords.
- Data Handling Procedures: Provide clear guidelines on how to handle customer data securely.
- Social Engineering Awareness: Educate employees about social engineering tactics.
- Security Policies and Procedures: Ensure that employees understand and follow your security policies and procedures.
- Regular Security Drills: Conduct simulated phishing attacks and other security drills to test employee awareness and response.
8. Secure Your Integrations and Third-Party Vendors
Your CRM system often integrates with other applications. Secure these integrations and vet your third-party vendors:
- Secure APIs: Use secure APIs (Application Programming Interfaces) to connect your CRM system with other applications.
- Regularly Review Integrations: Review your integrations regularly to ensure that they are still necessary and secure.
- Vendor Security Assessments: Assess the security practices of your third-party vendors before integrating with them.
- Data Sharing Agreements: Establish data sharing agreements with your vendors that outline how customer data will be protected.
9. Develop and Regularly Test an Incident Response Plan
An incident response plan outlines the steps you will take in the event of a security incident. Develop a detailed plan that includes the following:
- Incident Detection: How you will detect security incidents.
- Incident Response: The steps you will take to respond to a security incident.
- Containment: How you will contain the incident to prevent further damage.
- Eradication: How you will remove the cause of the incident.
- Recovery: How you will restore your systems and data.
- Post-Incident Analysis: A review of the incident to identify lessons learned and improve your security posture.
- Regular Testing: Regularly test your incident response plan to ensure that it is effective.
- Communication Plan: Include a communication plan for notifying customers, regulators, and other stakeholders in the event of a breach.
10. Stay Informed and Adapt to the Evolving Threat Landscape
The security landscape is constantly changing. You need to stay informed and adapt your security strategy accordingly. This includes:
- Following Security News and Blogs: Stay up-to-date on the latest security threats and vulnerabilities.
- Attending Security Conferences and Webinars: Learn from industry experts and network with other security professionals.
- Joining Industry Groups: Join industry groups to share information and best practices.
- Regularly Reviewing and Updating Your Security Policies: Review and update your security policies regularly to reflect the latest threats and best practices.
- Embracing Automation: Automate security tasks whenever possible to improve efficiency and reduce the risk of human error.
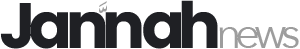
Choosing the Right CRM for Security in 2025
When selecting a CRM system, security should be a primary consideration. Look for a CRM provider that:
- Has a Strong Security Track Record: Research the provider’s security history and reputation.
- Offers Robust Security Features: Look for features such as MFA, encryption, access controls, and regular security updates.
- Complies with Industry Standards: Ensure that the provider complies with relevant data privacy regulations and industry standards.
- Provides Comprehensive Security Documentation: Review the provider’s security documentation to understand their security practices.
- Offers Security Training and Support: Make sure the provider offers security training and support to help you implement and manage your CRM security.
- Provides Regular Security Audits: Check if the CRM provider conducts regular security audits and penetration testing to identify and address vulnerabilities.
Building a Culture of Security
Security isn’t just about technology; it’s about culture. Create a culture of security within your organization by:
- Making Security a Priority: Make security a priority at all levels of your organization, from the CEO to the entry-level employee.
- Providing Regular Security Training: Provide ongoing security training to all employees.
- Encouraging Reporting: Encourage employees to report security incidents and concerns.
- Recognizing and Rewarding Security Best Practices: Recognize and reward employees who demonstrate strong security practices.
- Fostering Open Communication: Foster open communication about security issues and concerns.
- Leading by Example: Lead by example by demonstrating strong security practices.
The Future of CRM Security: Emerging Trends
The future of CRM security will be shaped by several emerging trends:
- AI-Powered Security: AI will play an increasingly important role in security, automating threat detection, incident response, and vulnerability management.
- Zero Trust Architecture: Zero trust security assumes that no user or device is trusted by default, and all access requests must be verified.
- Blockchain-Based Security: Blockchain technology can be used to secure data and prevent tampering.
- Increased Automation: Automation will be used to streamline security tasks and reduce the risk of human error.
- Focus on User Experience: Security measures will be designed to be user-friendly and not disrupt the user experience.
Conclusion: Securing Your CRM for a Secure Future
Securing your small business CRM in 2025 is not just a technical necessity; it’s a strategic imperative. By understanding the evolving threat landscape, implementing robust security measures, and fostering a culture of security, you can protect your valuable customer data, build trust, and ensure the long-term success of your business. Remember, the investment in security is an investment in your future. Don’t wait until it’s too late. Start fortifying your CRM today.