Fortifying Your Small Business: A Deep Dive into CRM Security

In the dynamic landscape of small business operations, customer relationship management (CRM) systems have evolved from a mere luxury to a fundamental necessity. These systems, meticulously designed to streamline interactions with clients, manage data, and boost sales, are now the bedrock of efficient and effective business practices. But as the reliance on CRM platforms intensifies, so too does the importance of fortifying their security. For small businesses, often lacking the expansive resources of larger corporations, robust CRM security isn’t just a best practice; it’s a matter of survival. This comprehensive article delves into the multifaceted world of CRM security, providing an in-depth exploration of the threats, best practices, and critical considerations that small businesses must embrace to protect their valuable data and ensure long-term success.
The Rising Tide of Cyber Threats: Why CRM Security Matters More Than Ever
The digital realm is a volatile place, and small businesses are increasingly attractive targets for cybercriminals. The shift to remote work, the proliferation of cloud-based services, and the sheer volume of sensitive data stored within CRM systems have created a perfect storm for potential breaches. Understanding the specific threats is the first step in building a resilient security posture.
Common Cyber Threats Targeting CRM Systems
- Data Breaches: This is perhaps the most devastating threat. Hackers aim to steal customer data, including personally identifiable information (PII), financial details, and communication records. A data breach can lead to significant financial losses, reputational damage, and legal repercussions.
- Ransomware Attacks: Cybercriminals encrypt a company’s data and demand a ransom for its release. CRM systems, being central hubs of critical business information, are prime targets for ransomware attacks.
- Phishing and Social Engineering: These attacks exploit human vulnerabilities. Cybercriminals use deceptive emails, websites, or phone calls to trick employees into revealing sensitive information, such as login credentials.
- Malware Infections: Malicious software can infect CRM systems, allowing attackers to steal data, monitor activity, or disrupt operations.
- Insider Threats: Not all threats come from external sources. Disgruntled employees, careless staff, or those with malicious intent can pose a significant risk to data security.
- Denial-of-Service (DoS) Attacks: These attacks aim to overwhelm a CRM system’s servers, making the system unavailable to legitimate users. This can disrupt business operations and lead to lost revenue.
The Impact of a CRM Security Breach on Small Businesses
The consequences of a CRM security breach can be catastrophic for a small business. Beyond the immediate financial losses, the long-term effects can be devastating.
- Financial Losses: Costs associated with a breach can include forensic investigations, legal fees, regulatory fines, credit monitoring services for affected customers, and the cost of restoring data and systems.
- Reputational Damage: A security breach can erode customer trust and damage a company’s reputation. This can lead to lost customers and difficulty attracting new ones.
- Legal and Regulatory Penalties: Businesses are legally obligated to protect customer data. Failure to do so can result in hefty fines and other penalties.
- Operational Disruption: A breach can disrupt business operations, leading to lost productivity and revenue. It can take days, weeks, or even months to fully recover from a significant breach.
- Competitive Disadvantage: A security breach can put a small business at a competitive disadvantage, as it struggles to regain customer trust and rebuild its reputation.
Essential Security Practices for Your CRM System
Protecting your CRM system requires a multi-layered approach. Implementing a combination of technical safeguards, robust policies, and employee training is crucial for minimizing risk and ensuring data security.
1. Strong Password Policies and Multi-Factor Authentication (MFA)
The foundation of any good security strategy is strong passwords. Enforce complex password requirements, including a mix of upper and lowercase letters, numbers, and special characters. Regularly update passwords and avoid reusing them across multiple accounts. Multi-factor authentication (MFA) adds an extra layer of security by requiring users to verify their identity using a second factor, such as a code sent to their mobile device. This significantly reduces the risk of unauthorized access, even if a password is compromised.
2. Access Control and User Permissions
Implement a strict access control policy. Grant users only the minimum level of access necessary to perform their job duties. Regularly review user permissions and remove access for former employees or those who no longer require it. This helps to limit the potential damage from insider threats or compromised accounts.
3. Data Encryption
Encryption is the process of converting data into an unreadable format, protecting it from unauthorized access. Encrypt sensitive data both in transit (when it’s being transmitted over a network) and at rest (when it’s stored in the CRM system). This ensures that even if a hacker gains access to the data, they won’t be able to read it without the decryption key.
4. Regular Backups and Disaster Recovery Planning
Data loss can occur due to various reasons, including hardware failures, human error, and cyberattacks. Implement a robust backup strategy to ensure that you can quickly restore your data in the event of a disaster. Regularly back up your CRM data and store backups in a secure location, separate from your primary system. Develop a disaster recovery plan that outlines the steps to take in the event of a data breach or other disruptive event. Test your backups and disaster recovery plan regularly to ensure they are effective.
5. Security Audits and Vulnerability Assessments
Conduct regular security audits and vulnerability assessments to identify weaknesses in your CRM system. These assessments can help you proactively address potential vulnerabilities before they are exploited by attackers. Hire a security professional or use specialized tools to scan your system for vulnerabilities, such as outdated software, misconfigured settings, and weak passwords. Address any identified vulnerabilities promptly.
6. Software Updates and Patch Management
Keep your CRM system and all related software up to date. Software vendors regularly release updates and patches to fix security vulnerabilities. Implement a patch management system to ensure that updates are applied promptly. This helps to protect your system from known exploits.
7. Network Security
Protect your CRM system by securing your network. This includes using a firewall to block unauthorized access to your network, implementing intrusion detection and prevention systems to detect and respond to malicious activity, and regularly monitoring network traffic for suspicious behavior. Segment your network to isolate your CRM system from other parts of your network, limiting the potential impact of a breach.
8. Employee Training and Awareness
Your employees are your first line of defense against cyber threats. Provide regular security awareness training to educate employees about common threats, such as phishing, social engineering, and malware. Train employees on how to identify and report suspicious activity. Foster a culture of security awareness throughout your organization.
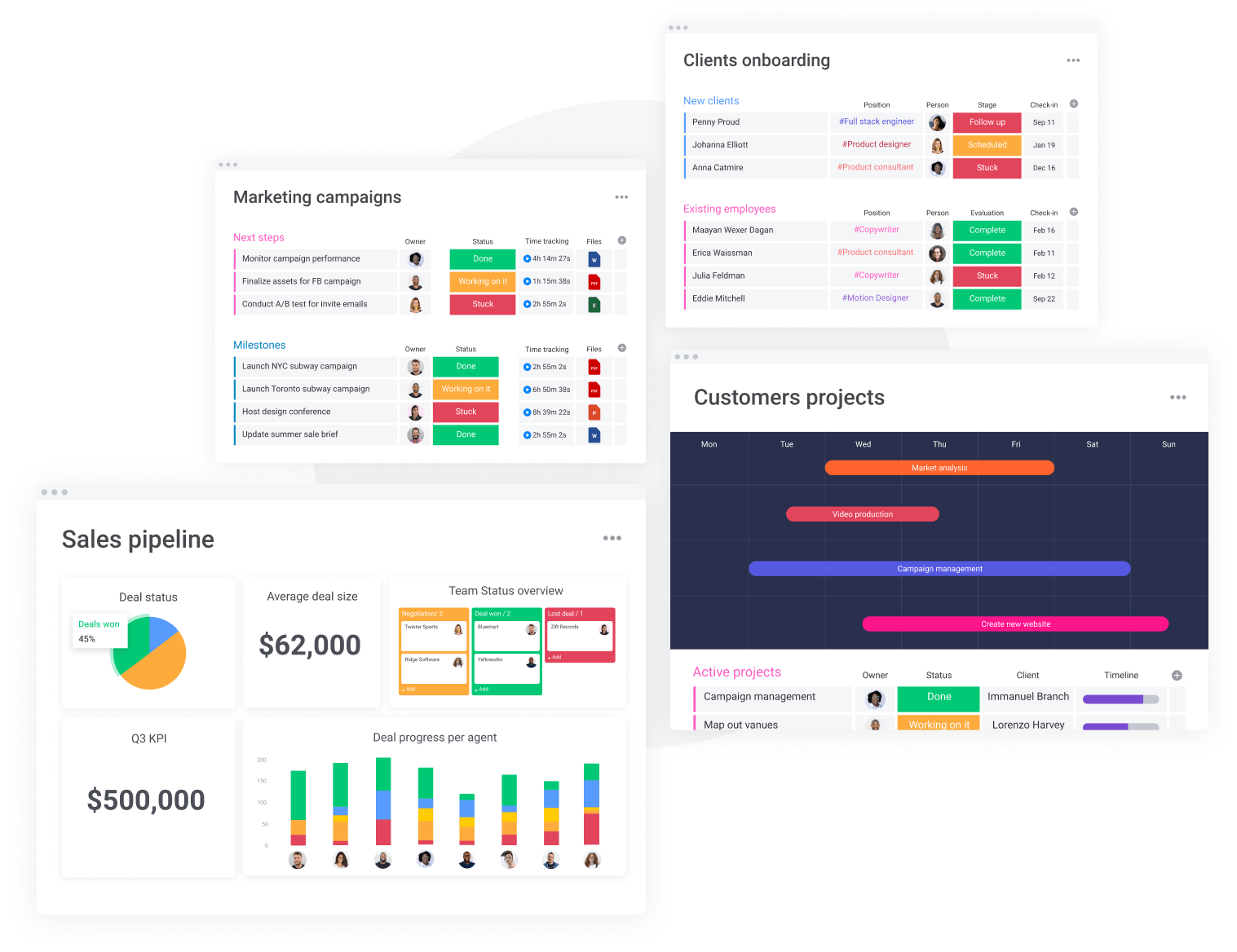
9. Choose a Secure CRM Provider
If you’re using a cloud-based CRM, choose a provider that has a strong reputation for security. Research the provider’s security practices, certifications, and compliance with relevant regulations. Ensure that the provider offers features such as data encryption, multi-factor authentication, and regular security audits. Carefully review the provider’s service level agreements (SLAs) to understand their security guarantees and data protection policies.
10. Incident Response Plan
Develop an incident response plan to outline the steps to take in the event of a security breach. The plan should include procedures for identifying and containing the breach, notifying affected parties, and restoring systems. Regularly test your incident response plan to ensure it is effective. Designate a team responsible for managing security incidents and provide them with the necessary training and resources.
Choosing the Right CRM for Security: Key Considerations
Not all CRM systems are created equal when it comes to security. When selecting a CRM platform for your small business, prioritize security features and consider the following factors:
Security Features
Look for a CRM system that offers robust security features, such as:
- Data Encryption: Both in transit and at rest.
- Multi-Factor Authentication (MFA): To protect user accounts.
- Access Control: Granular control over user permissions.
- Audit Trails: To track user activity and identify potential security breaches.
- Regular Security Audits: Conducted by independent third parties.
- Compliance with Security Standards: Such as SOC 2 or ISO 27001.
Data Residency and Compliance
If your business operates in a regulated industry or handles sensitive data, consider where the CRM provider stores its data. Ensure that the provider complies with relevant data privacy regulations, such as GDPR or CCPA. Data residency refers to the physical location where your data is stored. Some businesses may prefer data centers located within specific geographic regions due to legal or compliance requirements.
Vendor Reputation and Support
Research the CRM provider’s reputation for security. Read reviews, check for security certifications, and assess their commitment to data protection. Consider the provider’s support and maintenance offerings. Do they provide timely security updates and patches? Do they offer adequate support in case of a security incident?
Integration with Existing Security Tools
Ensure that the CRM system integrates with your existing security tools, such as firewalls, intrusion detection systems, and security information and event management (SIEM) solutions. This allows you to centralize security monitoring and incident response. Compatibility with your existing infrastructure is crucial for seamless integration and effective security management.
Scalability and Flexibility
Choose a CRM system that can scale to meet your business’s evolving needs. Consider the system’s flexibility and ability to adapt to changing security threats and regulations. The CRM should be able to grow with your business, accommodating more users, data, and features as your company expands. Flexibility is also important to adapt to evolving security threats and regulatory changes.
Real-World Examples: CRM Security Success Stories
Learning from the experiences of other small businesses can provide valuable insights and inspire effective security practices. Here are a few examples of how small businesses have successfully implemented CRM security measures:
Example 1: Implementing MFA and Access Controls
A small marketing agency implemented multi-factor authentication (MFA) for all user accounts in their CRM system. They also implemented strict access controls, granting users only the necessary permissions. This significantly reduced the risk of unauthorized access and data breaches. Their focus on user access management and strong authentication protocols created a more secure environment.
Example 2: Regular Security Audits and Employee Training
A small e-commerce business regularly conducted security audits and provided ongoing security awareness training to its employees. This helped them identify and address vulnerabilities in their CRM system and educate employees about common threats. Their investment in employee education and system assessments helped them to maintain a proactive security posture.
Example 3: Data Encryption and Backup Strategy
A small financial services firm encrypted sensitive data in their CRM system and implemented a comprehensive backup strategy. This ensured that their data was protected in case of a breach or disaster. Their focus on data protection measures provided them with data resilience.
The Future of CRM Security: Emerging Trends
The landscape of CRM security is constantly evolving. Small businesses should stay informed about emerging trends to anticipate and mitigate future threats.
Artificial Intelligence (AI) and Machine Learning (ML)
AI and ML are being used to enhance CRM security in several ways, including threat detection, anomaly detection, and automated incident response. AI can analyze vast amounts of data to identify suspicious activity and predict potential threats. This allows for proactive security measures and faster incident response times. ML algorithms can learn from past incidents and improve the accuracy of threat detection.
Zero Trust Security Model
The Zero Trust security model assumes that no user or device, whether inside or outside the network, can be trusted by default. This model requires all users to be authenticated and authorized before accessing any resources. This approach helps to minimize the impact of a security breach by limiting access to only the necessary resources. Zero Trust is gaining traction as a robust security framework for CRM systems.
Blockchain Technology
Blockchain technology can be used to enhance CRM security by providing a secure and transparent way to store and manage data. Blockchain can be used to create immutable audit trails, verify data integrity, and prevent unauthorized modifications. The use of blockchain can add an extra layer of security and trust to the CRM system.
Security Automation
Security automation involves automating security tasks, such as vulnerability scanning, patch management, and incident response. Automation can help small businesses improve their security posture by reducing the time and effort required to manage security tasks. Security automation can also help to improve the consistency and accuracy of security measures.
Conclusion: Securing Your CRM for a Secure Future
CRM systems are indispensable tools for small businesses, but their security is paramount. By understanding the threats, implementing best practices, and staying informed about emerging trends, small businesses can protect their valuable data, build customer trust, and ensure long-term success. Investing in CRM security is not just a technical requirement, it is a strategic imperative for building a resilient and thriving business in the digital age. The proactive implementation of security measures is an investment in your business’s future, safeguarding your data and ensuring the trust of your customers. Embrace a security-first mindset, and your small business will be well-positioned to navigate the complexities of the digital landscape with confidence and security.